Since TSplus Advanced Security 3.0 version, the Ransomware Protection enables you to efficiently DETECT, BLOCK and PREVENT ransomware attacks. TSplus Advanced Security reacts as soon as it detects ransomware on your session.
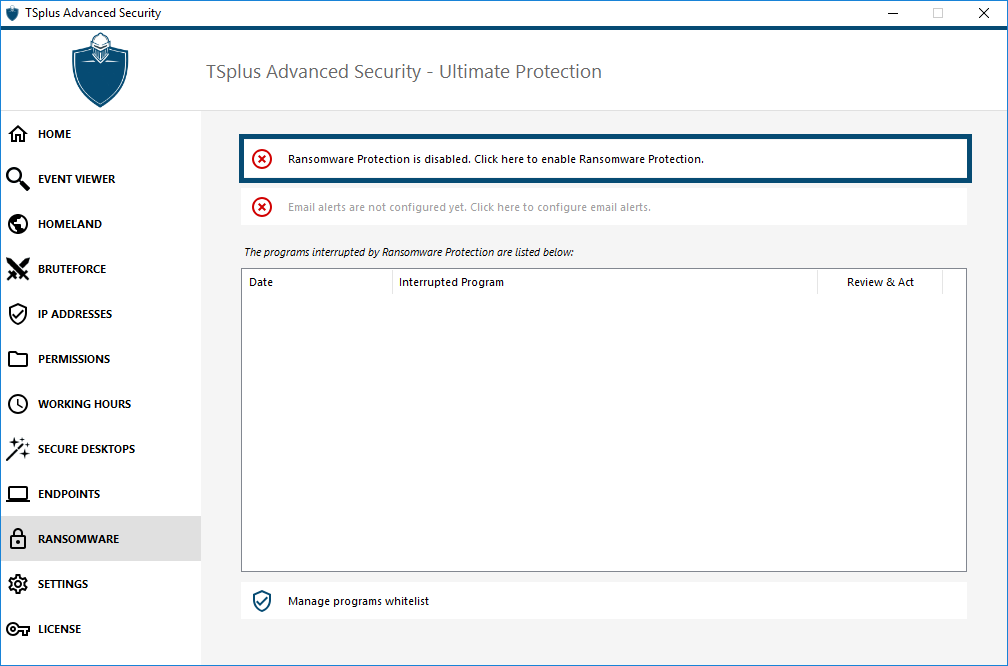
You can enable it by clicking on the “Enable Ransomware Protection” on the Ransomware Protection tab:
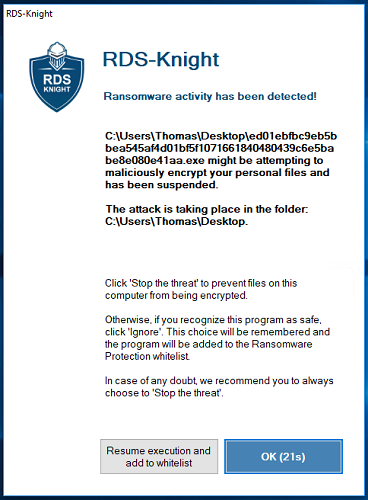
It quickly scans your disk(s) and displays the file(s) or program(s) responsible, in addition to providing a list of the infected items.
TSplus Advanced Security automatically stops the attack and quarantines the program(s) along with the file(s) encrypted before its intervention.
Only the administrator can whitelist them, by entering the path of the desired program on the bottom line and by clicking on “Add”:
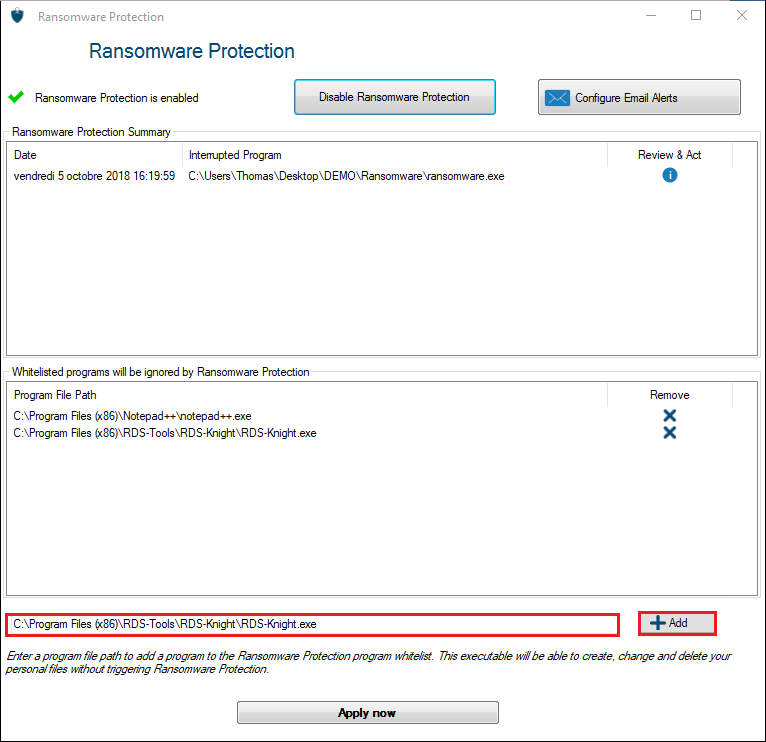
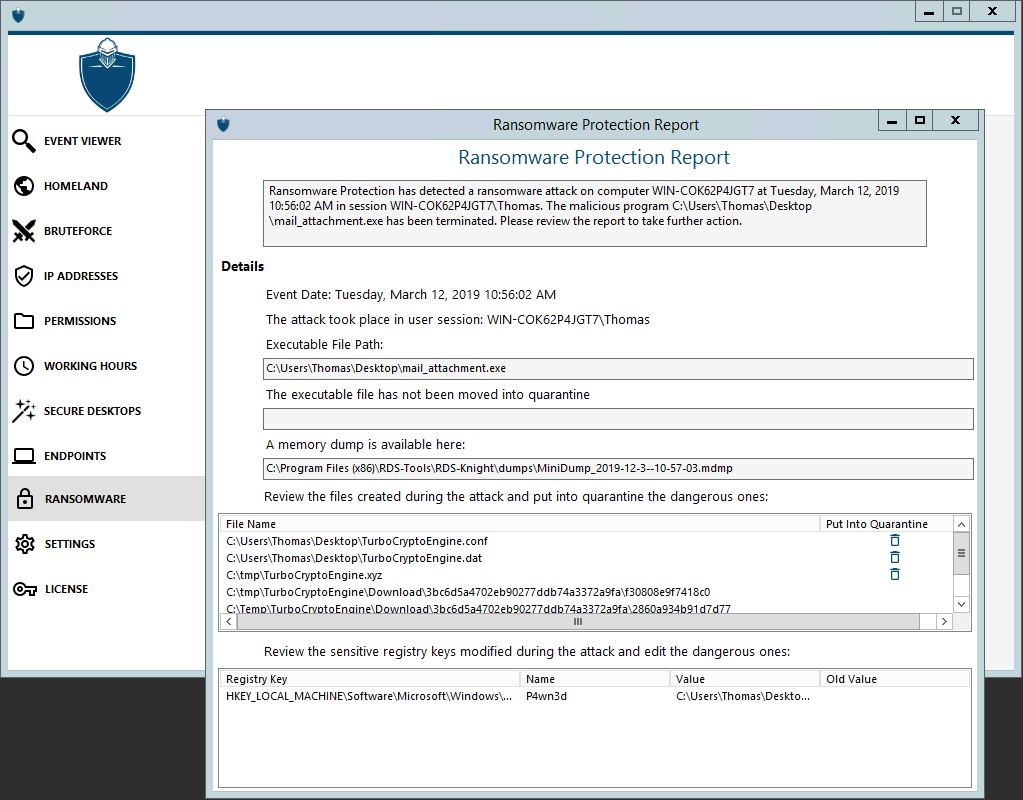
Ransomware Protection Report
TSplus Advanced Security prevents catastrophic events for businesses by removing ransomware at an early stage.
The administrator has access to information regarding the source of the attack and running processes, and therefore learns how to anticipate these threats.
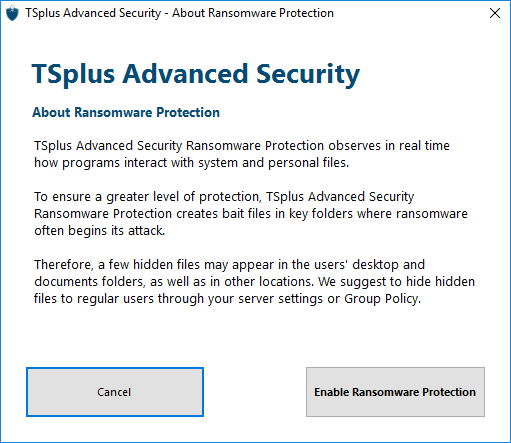
Note: Ransomware Protection observes how programs interact with system and personal files. To ensure a greater level of protection, Ransomware Protection creates bait files in key folders where ransomware often begins its attack. Therefore, a few hidden files may appear in the users’ desktop and documents folders, as well as in other locations. When it detects a malicious behaviour, it stops the ransomware immediately (or ask if the logged user is an administrator).
Ransomware Protection uses pure behavioural detection techniques and does not rely on malware signatures, allowing it to catch ransomware which does not exist yet.
Ransomware Protection Report
You can configure your SMTP settings in order for TSplus Advanced Security to send you email alerts to highlight important security events by clicking on the button below the Ransomware activation one:
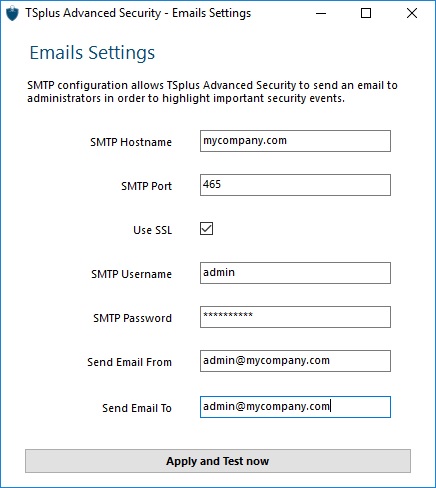
Enter your SMTP Hostname, Port and check the Use SSL box if you wish to use SSL.
Enter the SMTP Username and Password, as well as the sender and receiver addresses.
Email Settings can be validated by sending a test when saving SMTP settings.